However, TOR has been protecting people's identity from uncovering and letting them express their ideas over the internet anonymously. As the official Tor website (https://www.torproject.org/) says, the main users of this Tor network are Activists, Military and Law enforcements, Media and various other people for their tasks. Besides them people misuse this network to visit banned websites, download sexual content bypassing filters and most importantly, Tor network is now used by Hackers to attack organizations without revealing their identity. A most reason example for the later was the recent Skynet Botnet in which Command and Control Servers (C&C) hidden behind the Tor Network.
How Tor Works ?
Tor consists of a network of relay servers which are run by volunteers all over the world. When a user connects to the Tor network using Tor client/Tor enabled browser, a path is created from the user to the destination server to which the user needs to connect. This path consists of three relay servers called Entry Node, Middle Node and Exit Node.All the requests the sender sends to the destination through the Tor network are relayed through this pre-built path and the responses from the destination returns back to the sender through the same path. All the data going through the Tor network is completely encrypted such that nobody who intercepts the communication have no clue who the sender is. But, if one sniffs outgoing link from the exit node can capture the data transmitted both sides, but anonymity is still secured. I will later explain how this protection happens.
When you download Tor from the website, you can run Tor as a local SOCKS proxy in you computer. When your browser is configured to use that local SOCKS proxy, you can browser internet with that browser through the tor network. You can configure many applications to use this SOCKS proxy and use them through Tor network, these applications include web browsers, download manager software, bittorrent clients etc.
Bypassing Firewalls and Filtering mechanisms
When you are connected to a server via Tor network, your firewall or any filtering device only sees you are connected to a node of the Anonymous network, not to the actual server you are communicating with. And with the data encrypted, these filtering mechanisms cannot inspect inside the packets and cannot interpret the actual content. So these data is slipped through firewalls and filtering mechanisms.How Tor Protects Anonymity
Tor is an implementation of Onion Routing which provides a Multi-Layer encryption for users's data and relay through a network of Onion Routers. So what is onion routing?Say a users is connected to a destination server through a network of Onion Routers (or Relays). The data user sends to the destination server is encrypted in multiple layers so that each layer can only be decrypted by one onion router in the network. So if the user is connected to a destination through 4 Onion routers, the data sent is encrypted in 4 layers. In Tor Network, a user is connected to 3 nodes in the Tor network. Following diagram is taken from wikipedia which clearly show how data is encrypted in 3 layers.
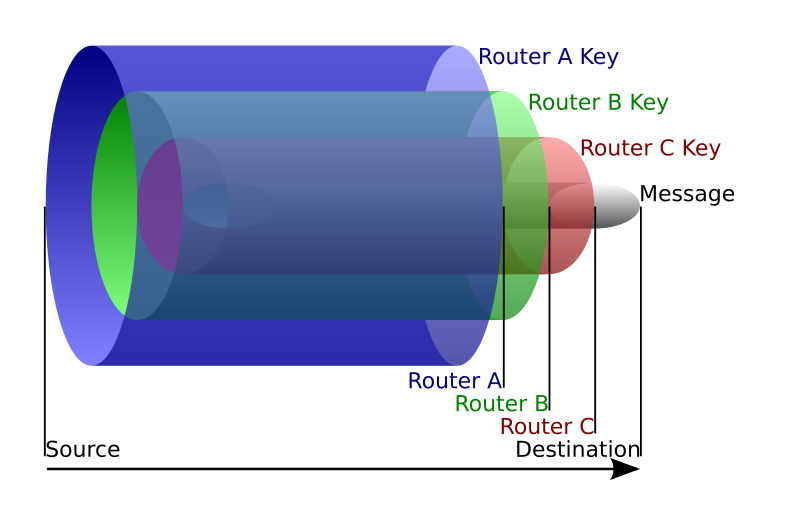
When a user connects using Tor as a proxy server, Tor finds 3 Nodes (Entry node, Middle Node and Exit Node) in the anonymous network. During this discovery, Tor also generates 3 seperate shared secret keys (symmetric keys) with each node using Diffie-Hellmann Key Exchange. Any router among these three has no idea about what other two's keys are. Only the sender has the three keys so that it can encrypt the data he sends in 3 layers. As the above diagram shows, once this 3-layer-encrypted data is sent through these three nodes, Entry node decrypts the first layer of the encryption using his shared secret key and discovers where to relay the data. But it has no capability to findout the actual data because it is encrypted using a key which it does not have. Then the 2-layer-encrypted data coming from the Entry Node is relayed to the Middle Node. Then it decrypts the next layer of encryption using its shared secret key as above described. And the decrypted data is relayed to the Exit node. The data coming to the Exit Node is only encrypted in One layer. So, when it is decrypted using Exit Node's shared secret key, the actual plain text data is revealed. Then this actual data is sent in plain text to the destination server.
So we have a clear security threat with these Exit nodes. If an Exit node is compromised or an exit node is run by a malicious party, the attacker has the capability to sniff all the traffic which comes out from the Exit node and capture sensitive information such as user credentials and bank information. So, for the maximum level of security, users are advised to visit websites using a secured HTTPS connection. Then the outgoing traffic from the exit node is also encrypted using a shared key which only the sender and the destination knows, attacker cannot identify the data.
I found a amazingly nice and clear graphics elabortion on how Tor works with and without HTTPS. This is created by Electronics Frontier Foundation. You can visit the original article here.
In a later post, I will describe following things in detail.
I try to describe this as comprehensive as possible so that readers can have a good idea of the whole process. There are thousands of thousands of articles and blogs written about this but, most articles describe on only one portion of the process. So I think it would be better to give a complete series of posts about the whole process. Please post comments if you have any more things to add or any corrections to be made.
Thank you.
I found a amazingly nice and clear graphics elabortion on how Tor works with and without HTTPS. This is created by Electronics Frontier Foundation. You can visit the original article here.
In a later post, I will describe following things in detail.
- Node discovery using directory servers
- Sharing secret keys using Diffie Helmann Key Exchange
- Wireshark analysis of Tor connection establishment
- Security Threat in Tor network
- How anonymity breaks when using tor in uneducated manner
- Cases that hackers used Tor network for attacks.
I try to describe this as comprehensive as possible so that readers can have a good idea of the whole process. There are thousands of thousands of articles and blogs written about this but, most articles describe on only one portion of the process. So I think it would be better to give a complete series of posts about the whole process. Please post comments if you have any more things to add or any corrections to be made.
Thank you.
0 comments:
Post a Comment
Note: Only a member of this blog may post a comment.